Home
> FAQs
> Comptes, Autenticació i Seguretat
> Com evitar ser víctima del phishing
Com evitar ser víctima del phishing
QUÈ ÉS EL PHISHING?
El phishing és una de les tècniques més utilitzades actualment pels Ciberdelincuents. És una forma de frau per Internet on els ciberdelinqüents intenten enganyar a l'usuari per a obtenir informació personal o confidencial, normalment mitjançant l'enviament de correus electrònics, missatges SMS o trucades telefòniques que semblen completament legítims.
Davant d'aquesta amenaça tot el personal de la institució haurà d'estar alerta per a no caure en la trampa del phishing, ha de saber identificar un missatge o correu electrònic fals i ha d'informar ràpidament el departament de sistemes en cas de detecció o sospita.
|
Davant el mínim dubte DESCONFIA i REPORTA!
|
COM EVITEM SER VÍCTIMES DEL PHISHING?
Les millors eines que tenim per a defensar-nos són el sentit comú i la precaució.
Hem de tenir sempre presents certes precaucions importants de cara a no ser víctimes del phishing, les quals són, principalment:
- No obrir emails sospitosos
- No clicar mai sobre enllaços (enllaços) que ens envien per email o SMS sense abans avaluar si poden ser sospitosos.
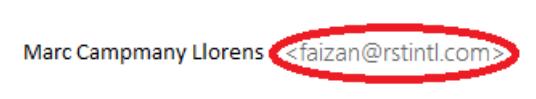
- Revisar sempre qui és el remitent real d'un email. Encara que el nom i cognoms puguin semblar correctes sempre hem de verificar que l'adreça de correu electrònic original sigui la corresponent.
- Comprovar que tota la informació del mail sigui coherent. Davant de qualsevol detall que no quadri (número de telèfon desconegut, idioma diferent, expressions poc comunes, enllaços d'internet sospitosos...) DESCONFIA i INFORMA.
- Mai proporcionar informació personal (usuaris, contrasenya, PIN…) o confidencial per email o telèfon.
Els ciberdelinqüents sempre intentaran FER-NOS CAURE EN LA TRAMPA mitjançant diferents tècniques:
- Ens enviaran un email falsejant qui envia el missatge, fent-nos creure que prové d'algú que coneixem.
- Ens posaran pressa dient que la informació caduca ràpidament o que perdrem l'accés a certa informació.
- Ens enviaran un fitxer adjunt o un enllaç maliciós perquè l'obrim.
En el cas que algú obri el fitxer o faci clic a l'enllaç adjunt el malware pot actuar de moltes maneres:
- Un malware del tipus “ransomware” que encriptarà tota la nostra informació i ens demanarà un rescat econòmic per a poder recuperar-la.
- Ens pot robar credencials bancàries.
- Ens pot robar les conversacions que hem tingut per email i els contactes que tenim, els quals utilitzaran per a enviar emails als destinataris d'aquestes conversacions per a fer encara més creïbles que els emails són reals.
- ENS PODEN INFECTAR l'ORDINADOR AMB TAN SOLS FER CLIC A L'ENLLAÇ SENSE QUE REALITZEM CAP ACCIÓ DINS LA PÀGINA.
APRENEM AMB EXEMPLES
Suposem el cas que rebem el següent email:
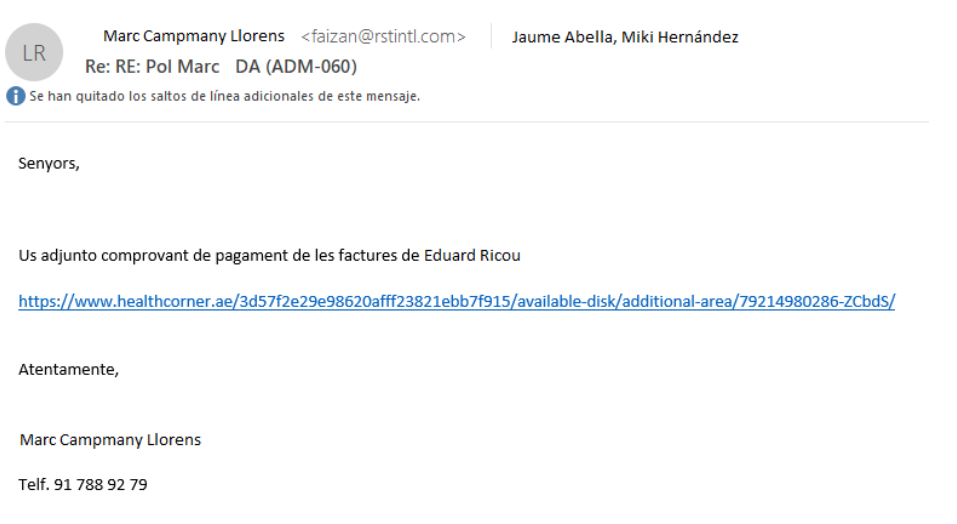
Aquest email, a primera vista, sembla del tot correcte, ja que és una resposta a una conversació prèvia. Però no, aquest email és maliciós.
Desafortunadament per a nosaltres el ciberdelinqüent ha tingut (fictíciament) accés a emails anteriors i els està utilitzant per a intentar enganyar als usuaris d'aquesta conversa.
Detalls en els quals ens haurem de fixar SEMPRE que rebem un email:

- Revisa en detall qui és el remitent del mail, tant el nom com l'adreça de correu electrònic. En el mail anterior podem veure que en el nom apareix algú de l'organització, però si ens hi fixem en la direcció de mail veurem que no pertany a l'organització:
- . Podem observar com el mail incorpora un enllaç d'Internet. En aquests casos, abans de clicar sobre un enllaç, s'ha de REVISAR SEMPRE la direcció real del enllaç, SITUANT el RATOLÍ sobre el link SENSE CLICAR.

-
Podem observar que la direcció de l'enllaç és totalment desconeguda (el domini healthcorner.ae no és un domini corporatiu) i, per tant, absolutament sospitós.
- També podem veure que el número de telèfon no correspon amb cap de la institució, ni tan sols és de la província de Barcelona. Novament, un altre detall que ens ha de fer sospitar.

|
RECORDA, MAI FACIS CLIC EN UN ENLLAÇ D'UN EMAIL SENSE ABANS HAVER REVISAT SI ÉS SOSPITÓS!!!
Davant la mínima sospita DESCONFIA i REPORTA!
|
Altres tipus de missatges dels quals, en primera instància, Hauríem de desconfiar:
-
Missatges que requereixen urgència.
-
Missatges que ofereixen “gangues” o ofertes.
-
Missatges que ens poden introduir, modificar o confirmar dades personals:
direccions personals, credencials d'accés, contrasenya, PIN, núm. de compte bancari, etc.
QUÈ HEM DE FER SI SOSPITEM D'UN PHISHING: REPORTAR
En el cas de tenir clar o de la mínima sospita, que estem sent víctimes d'un phishing hem d'informar ràpidament a Serveis TIC realitzant aquestes accions:
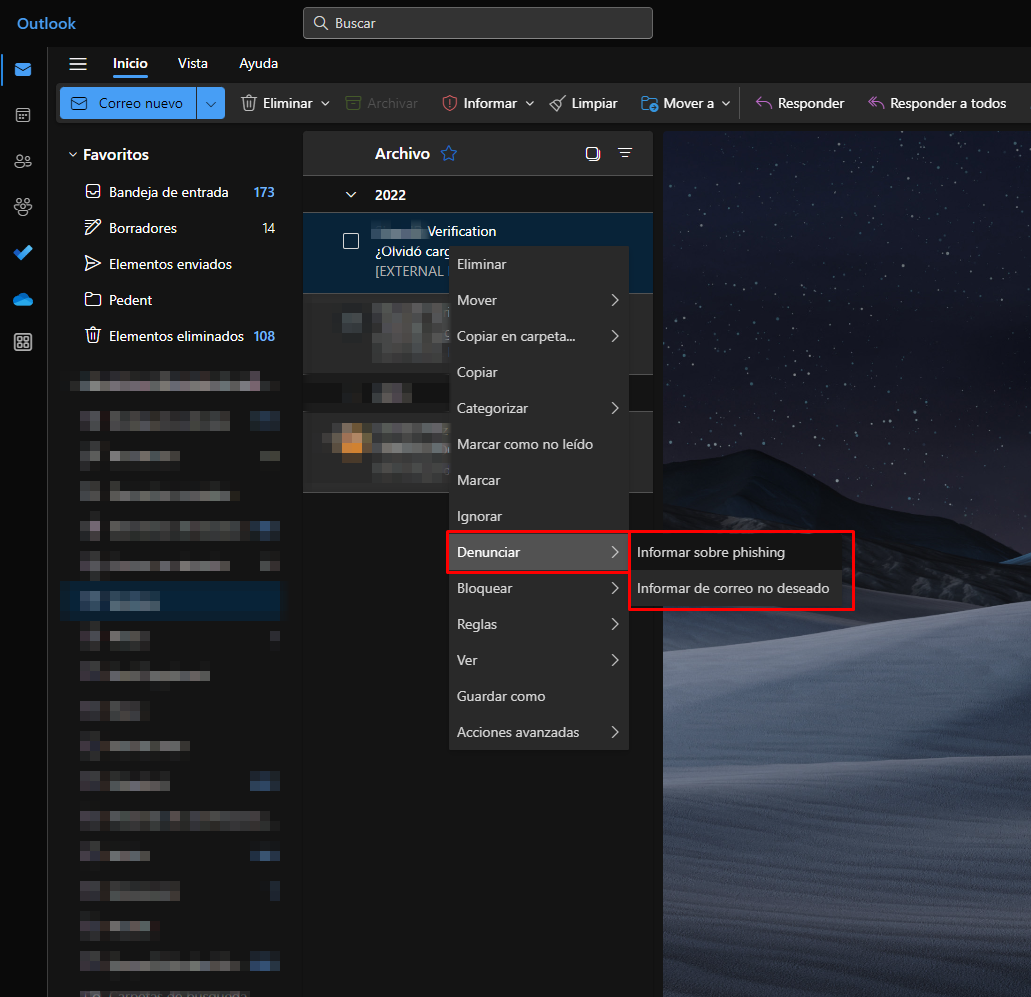
En aquest cas haurem d'accedir a https://outlook.office365.com/mail/ i continuar amb els passos següents:
-
Si tenim Outlook Modern/New o estem al navegador
1. A la llista de correus, fem clic amb el botó dret al correu
2. Seleccionem “Denunciar” o “Report” i a continuació “Informar sobre phishing” o “Informar de correu no desitjat”.
-
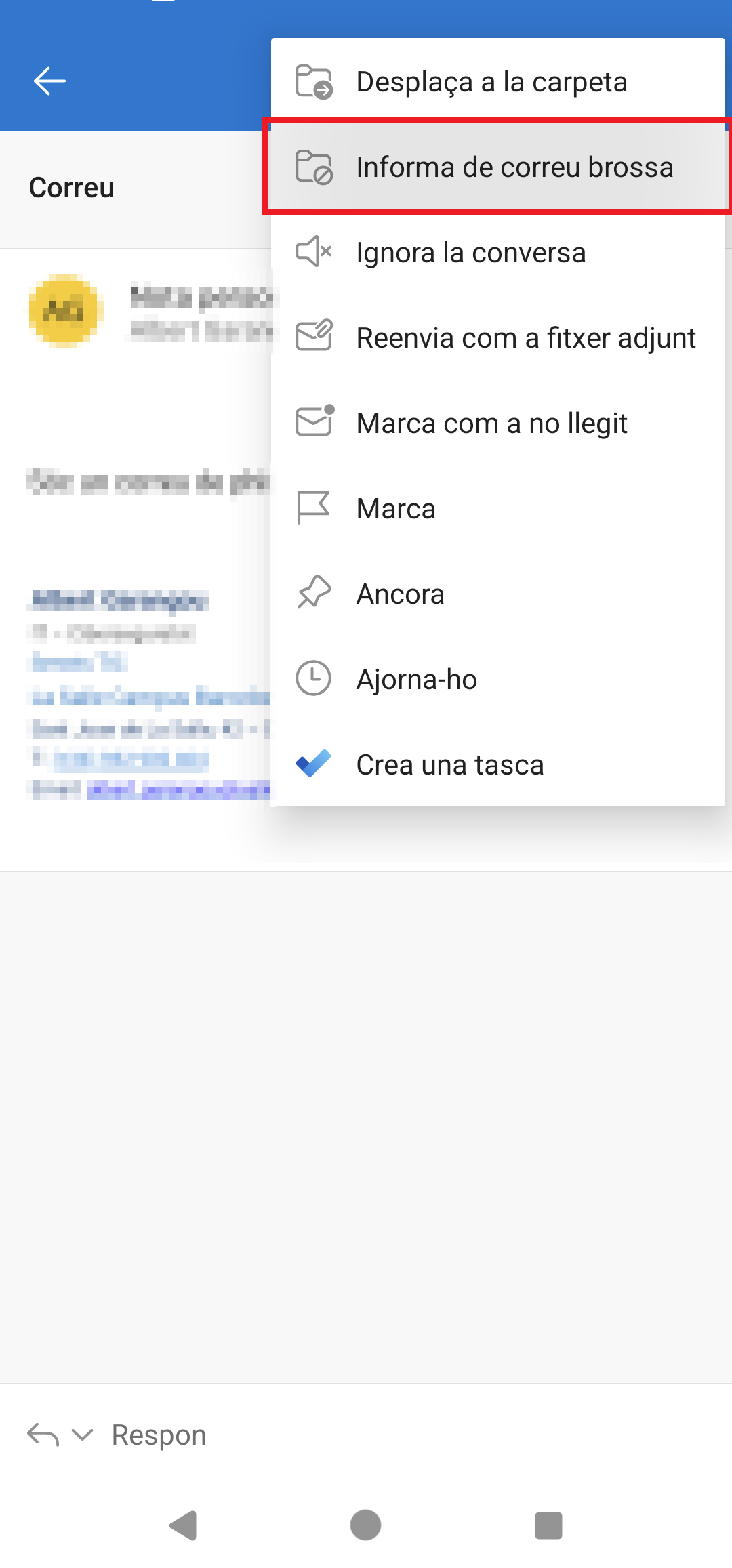
Si tenim Outlook al mòbil
1a. Si estem al llistat de correus: mantenim premut el correu per seleccionar-lo i premem els tres punts verticals per veure més opcions.
1b. Si estem dins el correu, premem els tres punts verticals per veure més opcions.
2. Seleccionem l'opció "Report Junk" o "Informa de correu borssa"